Friend spam or contact harvesting is when a company manipulates a user to give access to their private information, especially their contact list making it seem to the user that it would be beneficial for them but which the company later uses for its own benefit. It gets worse when the user finds out that their contact list has been spammed by the company in the user’s name.
Stuti Mazumdar & Symran Bhue - April 2022

How this pattern gets its name?
How this pattern gets its name is pretty self-explanatory. It typically starts when a product or platform gains access to a user’s address book by making it seem like it was in their best interest; for example, connecting with their friends. And once the product has access, it spams the user’s contact list using their contact no., email or social media account in pursuit of a performance metric.
How to identify this pattern?
This dark pattern can be asymmetric and deceptive at the same time. The metric which may be getting prioritised here is ‘new sign ups’. First, the user is guided through a series of steps where they give access to their address book. There may be an option to skip; however, due to the asymmetric nature of options presentation as well as the use of deceptive language, the user is forced to click through all the steps and give up information that they may not have originally intended to give up.
Examples
Prior to being acquired by Microsoft in 2016, LinkedIn was actively and aggressively friend spamming.
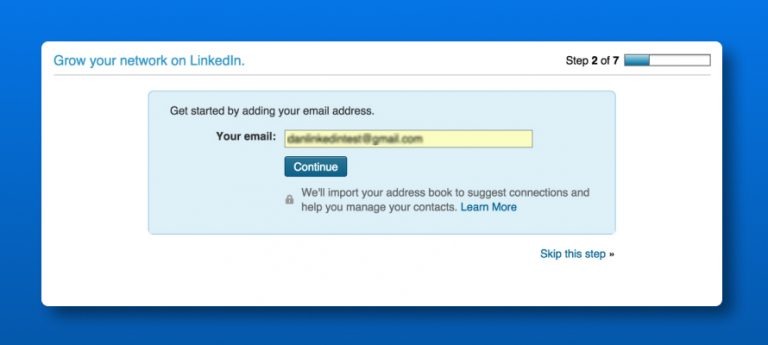
In 2014, LinkedIn subscribers assumed that they had to import their address books to the platform to continue using the service though it was optional.
However, many users, on realising that the social media platform was spamming their contacts in their name started growing increasingly against the platform which resulted in a lawsuit and eventually a fine of $13 million dollars in 2015 for LinkedIn.
How to make it an ethical design pattern?
The reason friend spam is a dark pattern is that it doesn’t present the user with clear options and doesn’t inform the user of the outcome. An easy fix – full disclosure. Informing the users accurately and honestly of the outcome or even taking their consent before sending out auto-emails to their address books is the first step. Second, allowing users to send custom messages and even select whom to email and whom to leave out will make the user experience a little more user-centric by moving control over to them rather than the product retaining it.




